Overview of DeFi Hacks and Security Concerns
Decentralized finance (DeFi) has emerged as a transformative force in the financial landscape, offering unprecedented opportunities for users to engage with financial services outside traditional banking systems. However, as the popularity of DeFi protocols has surged, so too have the vulnerabilities associated with them. Reports indicate that despite a decrease in the total amount stolen in 2023, hacks within the DeFi sector remain a significant threat, highlighting a persistent issue of security that needs urgent attention.
Insights from Halborn’s Report
A recent report by blockchain security firm Halborn sheds light on the alarming trends surrounding DeFi hacks from 2016 to 2023. The report details that the cumulative losses from the top 100 hacks during this period have reached a staggering $7.4 billion. The majority of these attacks have predominantly targeted popular blockchain networks, particularly Ethereum, Binance Smart Chain, and Polygon.
Types of Attacks and Their Impact
While on-chain hacks, such as smart contract exploitation, price manipulation, and governance attacks, are the most common forms of attack, the report highlights a concerning trend regarding off-chain attacks. These off-chain attacks, which include private key thefts, accounted for 29% of the total number of attacks and represented 34.6% of the funds stolen overall. Notably, in 2023, off-chain attacks surged, making up 56.5% of the total attacks and resulting in 57.5% of the stolen amount.
The Importance of Security Measures
One critical finding from the Halborn report is that only 21% of the hacked protocols employed multi-signature (multi-sig) wallets. Multi-sig wallets require multiple approvals for transactions, offering an added layer of security. This statistic raises questions about the security practices in place among DeFi protocols and emphasizes the need for more robust protective measures.
Auditing and Faulty Input Validation
Halborn also warns that the majority of on-chain attacks targeted protocols that had not undergone proper audits. The absence of thorough auditing processes leaves vulnerabilities that can be easily exploited by malicious actors. Furthermore, the report highlights that the lack of proper input verification and validation mechanisms in smart contracts is a significant contributor to losses due to exploitation. This underlines the critical need for developers to prioritize security audits and implement stringent validation protocols in their smart contract designs.
Emerging Threats: Cross-Chain Bridges
Cross-chain bridges, which allow users to transfer assets between different blockchain networks, have emerged as a key attack vector for cybercriminals. Halborn advises protocols to conduct comprehensive code reviews before utilizing any cross-chain bridge, as these bridges can introduce complex vulnerabilities that attackers can exploit. The Ronin Bridge hack, which recently resulted in a loss of $12 million, serves as a stark reminder of the risks associated with cross-chain protocols, especially in light of a previous $625 million exploit of the same protocol two years ago.
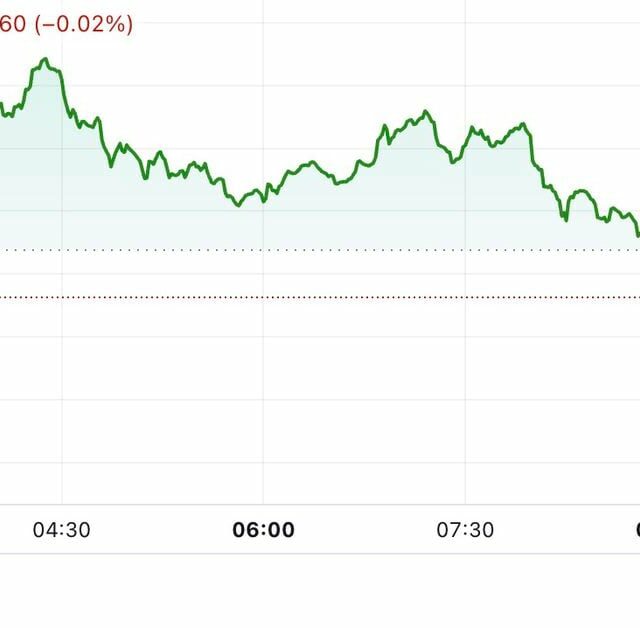
The Current Landscape of DeFi Hacks
According to an Immunefi report released earlier this year, hacks targeting the DeFi space led to losses totaling $473 million in the first half of 2024 alone. This figure underscores the ongoing threat posed by malicious actors and the critical need for enhanced security measures in the DeFi sector. As the landscape continues to evolve, it is imperative for developers, investors, and users alike to remain vigilant and proactive in addressing security vulnerabilities.
Conclusion
In conclusion, while DeFi offers innovative financial solutions, the associated risks cannot be overlooked. The data from Halborn and Immunefi highlight the urgent need for improved security protocols, thorough audits, and the adoption of multi-sig wallets across DeFi projects. By taking these steps, the industry can work towards mitigating risks and fostering a more secure environment for all participants.